As part of our upcoming visit to the International Cyber Fair & amp; International Security Expo, we were fortunate to sponsor a Series of cyber security webinars with Nineteen Group and Gray Hare Media.
Both Philip Ingram MBE and Emanuel Ghebreyesus, Director of Strategic Accounting for Tripwire, spoke on several topics, including:
Below you can read some of the highlighted things from their conversation.
Phillip Ingram: Today I have the pleasure of talking to Emanuel Ghebreyesus, who is the Strategic Director of Accounts for the British Government, Nuclear and Critical National Infrastructure (CNI) with Tripwire. Nice to see you this morning, Emmanuel.
Emanuel Ghebreyesus: Thank you for receiving me, Phillip.
PI: Given the growing complexity of cybersecurity, especially for government organizations and small and medium-sized enterprises (SMEs), what are some of the best ways to combat threats and increase trust?
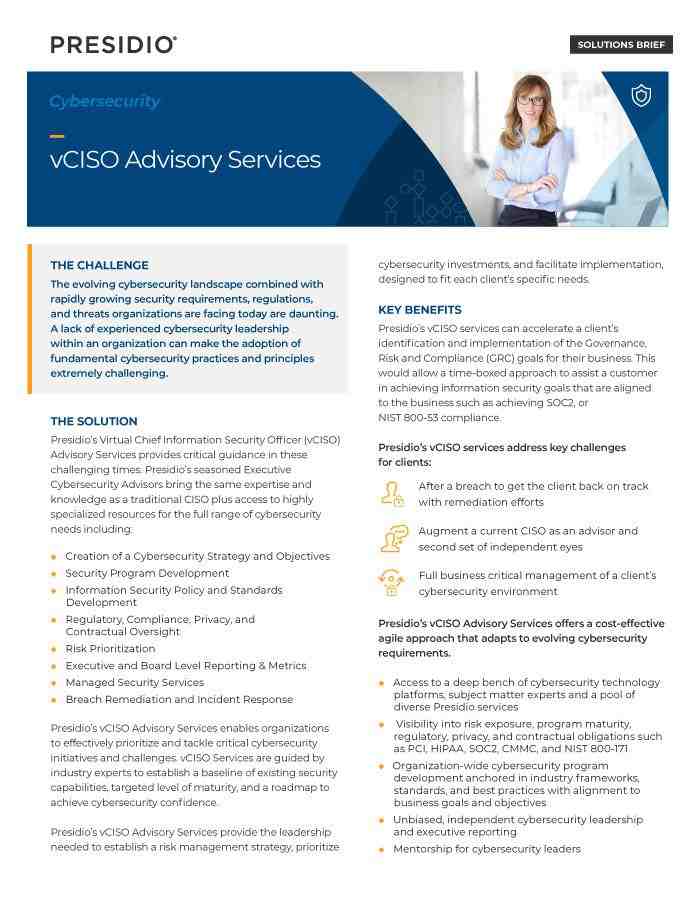
EG: That’s a very good question. There are a few things that almost everyone encounters on a daily basis in information technology (IT) and operational technology (OT) protection. Complexity is one of those constants. Therefore, a violation is possible. What organizations can do is work on how to deal with the violation when it happens in a very timely manner. To reach that level, these organizations must accept that violation is a very real risk. They must then take a step back, assess and understand what they are currently scheduled to do, and discuss how they can deal with the event when it occurs. My advice is to have a Chief Information Security Officer (CISO) available to answer these questions.
PI: The CISO function seems to expand over time. How do you view this growing responsibility in insuring an organization from attack?
Eg: A CISO must be able to create a policy with the Board and with the Chief Information Officer (CIO) on which the organization can work. These rules may include, for example, responses to data breaches and / or instructions on how to resolve vulnerabilities. The details of this policy will vary depending on how responsibility is assigned, how many team members are available, what technologies are applied, and how much of those technologies are actually integrated into each other.
Remember that many of these technologies collect data. So with that integration, if we throw all that data into one central database where the administrative team has to go and look for it, they won’t be able to be very effective if a breach happens. Lack of centralized information makes the organization more vulnerable. So instead of just throwing all kinds of technology at your current estate, it’s better to have effective solutions. For example, when conducting an investigation, you may need a vulnerability management solution, a file integrity monitoring solution, a SIEM solution, and / or a ticket sales solution. Everyone needs to support mutual integrations so that you can create one focal point where you observe your world.
PI: So you recommend the right set of integrated tools as a means of mitigating the burden on security teams?
EG: Many people in the industry call this your “glass pane” on your property. By understanding exactly what is going on and discovering the property, you get information about what is there. Basically, organizations need to look at the best solutions. The simple fact is that when you have these types of solutions working together, chances are your IT and OT teams can work more efficiently to solve any problems.
Another element of this is education. There are many people, even within the IT industry, who do not know how their personal devices or risky behavior on the Internet can endanger an organization. CISOs and administrators have to fix things 100% of the time, but criminals only need one chance. If they get in there, they will sit quietly and wait for a convenient moment to take action.
PI: Threats and attack techniques seem to be changing. What is your attitude?
EG: We have many different threats with the creation of new strains of ransomware and malicious actors demanding increased payments from hacked organizations. They are very smart criminals. As such, they are increasingly turning their attention to national infrastructure because everyone, especially bad actors, knows that there are many inherited systems that are not patched.
PI: I think you have covered the challenges in providing cyber security solutions. But there is a debate about considering different cyber solutions that are dedicated to their own capabilities or that manage services. What do you think is better and why?
EG: It depends on the type of organization you are in. There are advantages and disadvantages to any managed service. There are both advantages and disadvantages to any organization that does everything internally.
As for the benefits of managed services, one is to get a team that knows how to do what it takes. They are always on duty, 24 hours a day. The downside is that you won’t have that constant interaction with the managed service provider that you would have with the internal team, and if something goes wrong and your service level agreement with that managed service organization is out of place, what is your disaster recovery strategy ? Do you have a high availability solution so your business doesn’t just stop? All of these topics need to be considered, but obviously, if you have multiple professional procurement teams that understand contracts, who can ask these difficult questions to managed service providers, and who can deal with the little things. The contract should look like this, then you can get the right to that partnership.
Another strategy to have everything in the house is to hire a team. If something goes wrong, you can take action against the incident. But you have to make sure they are trained. A company cannot train one person for 75 different applications. It is a recipe for burning a person. However, with a pet you get a professional who manages your property. This helps ensure that data is stored where you want it. Thus, there are advantages and disadvantages of both approaches.
PI: How can organizations get the best out of their managed service providers?
EG: “Examine us” is what I say. Obviously, when Tripwire talks to an organization about managed services, all the teams are completely interconnected — our technical team, the R&D team, the account managers, the managers, and the vice presidents. Everyone is engaged because we have to make sure we fulfill every thing that the organization needs.
Tripwire’s solutions are very good at doing what they do. They are the best of the breed. But understanding these solutions as if doing exactly what the organization needs is most important. As long as we put this in the managed service document and the contracts that need to be signed, we will hit every point that is needed under that contract.
Our technical support services are also outstanding. We have a satisfaction rate of 97%, in part because we are always available to them. For example, if one of my customers has a problem, I have a direct number to call the research and development team or the product management team. I always have my system engineer and our consultants with me.
At the same time, it is clear to us what we can and cannot do. We therefore advise as we go and talk to our clients about the managed service. We educate ourselves at the same time as providing the service they need.
PI: It was a real pleasure to talk to you.
EG: Thank you so much for receiving me.
Want more insight into our webinar series? If so, you can watch the series on demand and review the responses of Professors Ciaran Martin, Nicole Whiting MBE and others by clicking here: https://www.internationalcyberexpo.com/nineteen-group-on-demand.
To learn more about Tripwire’s managed services in general, click here: https://www.tripwire.com/services/managed.
Cybersecurity is the protection of Internet-connected systems, such as hardware, software, and data, from cyber threats. … A strong cybersecurity strategy can provide a good security stance against malicious attacks designed to access, modify, delete, destroy, or extort systems and sensitive data of an organization or user.
What are the 5 benefits of using cyber security?

disadvantages and advantages of cyber security Read also : Spending on Managed Services, Especially Security, To Inch Up in 2022.
- Protects the system from viruses, worms, spyware and other unwanted programs.
- Data theft protection.
- Protects your computer from hacking.
- Reduces computer freezing and crashing.
- Gives privacy to users.
What is the main purpose of cyber security? Cybersecurity is the way individuals and organizations reduce the risk of cyber attacks. The basic function of cyber security is to protect the devices we all use (smartphones, laptops, tablets and computers) and the services we access – both online and at work – from theft or damage.
What are the benefits of good cyber security?
1) Protects the system from viruses, worms, spyware and other unwanted programs. 2) Protection against data theft. To see also : Managing Your Cloud: 5 Benefits of Managed Services | eWEEK. 3) Protects your computer from hacking. 4) Reduces computer freezing and crashing.
What is cyber security and its importance?
Cyber security refers to protecting systems connected to the Internet from threats in cyberspace. It includes protection for software, data, and hardware, and prevents cybercriminals from accessing devices or networks.
Why is Cyber security useful?
Cyber security is important because it protects all categories of data from theft and damage. These include sensitive data, identity disclosure data (PII), protected health data (PHI), personal data, intellectual property, data, and government and industry information systems.
Why is cybersecurity management important?
Cyber security is important because it protects all categories of data from theft and damage. On the same subject : Managed IT Services. These include sensitive data, identity disclosure data (PII), protected health data (PHI), personal data, intellectual property, data, and government and industry information systems.
What is cyber security and its significance? Cyber security refers to protecting systems connected to the Internet from threats in cyberspace. It includes protection for software, data, and hardware, and prevents cybercriminals from accessing devices or networks.
What is the biggest threat to computer security?
1) Phishing attacks The biggest, most harmful and widespread threat faced by small businesses are phishing attacks. Phishing accounts for 90% of all violations faced by organizations, has grown 65% in the past year, and accounts for more than $ 12 billion in business losses.
What is the biggest threat to computer security? The biggest security threats to endpoints identified in the survey were: negligent or negligent employees who do not follow security policies – 78% of personal devices connected to the network (BYOD) – 68% of employee use in commercial cloud applications workplace – 66%
What is a soar tool?

SOAR refers to technologies that enable organizations to collect input data overseen by a security operations team. SOAR tools allow an organization to define incident analysis and response procedures in a digital workflow format. …
What is Cyber security salary?
| Job title | Salary |
|---|---|
| Boeing Cyber Security salaries – reported 5 salaries | 102,000 USD / year |
| U.S. Federal Government Cyber Security Salaries – 4 salaries reported | 129.646 USD / year |
| Salaries IBM Cyber Security – 4 salaries reported | 32 USD / hour |
| Booz Allen Hamilton Cyber Security salaries – 3 salaries reported | 90,000 USD / year |
Are cyber security jobs well paid? Cyber Security Analyst The average cyber security salary for this position drops between $ 90,000 and $ 160,000, and is worth every penny. These security experts help create, plan, and implement security measures to keep your infrastructure secure.
Is cyber security a good career?
According to KPMG, the annual fee for cyber security bosses ranges from 2 Cr to 4 Cr per year. The industry also reports a satisfaction level of 68%, making it a career that mentally and financially satisfies most.
Is Cyber security in demand?
For the third year in a row, the role of cybersecurity analyst ranks as the first runner-up for the most sought-after security position. … According to the U.S. Bureau of Labor Statistics, cybersecurity analyst jobs are expected to grow 31 percent by 2029, about 5 times faster than the national average for job growth.
Is it hard to get a job in cyber security?
It’s not hard to get a job in cyber security. … Most recruitment managers emphasize soft skills for beginning candidates with most of the technical skills learned on the job. Individuals interested in Internet technologies will find a specialization in cybersecurity a useful career path.
How much do you make in cyber security?
The highest salary for Cyber Security in Canada is $ 147,450 per year. The lowest salary for cyber security in Canada is $ 43,369 per year.
How much do you make a year in cyber security?
It’s no secret that cybersecurity jobs are often very well paid. In fact, the average base salary of a cybersecurity expert in the U.S. is about $ 103,000 a year.
How much do cyber security earn per hour?
Cybersecurity in your area earns an average of $ 56 per hour, or $ 1.29 (2%) more than the national average hourly wage of $ 54.31.